Next-Generation Perimeter Defence for UAE Data Center Security
The UAE has established itself as one of the biggest digital hubs in the Middle East and the hyperscale projects are decentralising to both Dubai and Abu Dhabi. Because financial institutions, businesses, and government agencies depend on secure infrastructure for digital and a strong the security of data centres in the UAE are now the top priority of national security.
Data centres of the future must guard from both cyber and physical security threats. An approach to perimeter defense that is multi-layered makes sure that threats are detected, handled, and monitored on every level, starting with the outer boundaries and moving to racks for servers and data streams that are encrypted.
The Conceptualization Multi-Layer Perimeter Defense
Multi-layer approaches involve implementing layers of security that overlap in order that even when one layer fails, the other layer remains in place. When it comes to UAE establishments, it means:
- Physical boundary safeguarding
- Systems for controlling access
- Network-level protection
- Monitoring in real-time and automatization
Through integrating data center perimeter security and intelligent monitoring devices, companies can create an entire shield for crucial IT infrastructure.
1. Enhancing the Physical Perimeter
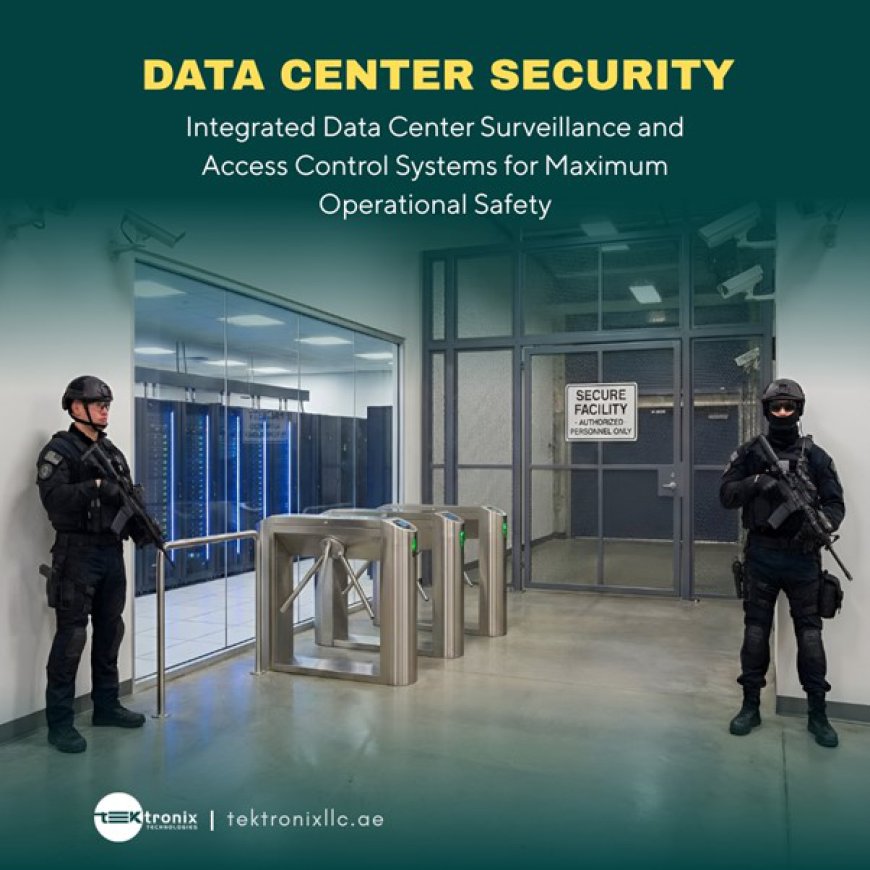
The initial defense line starts at the outside of the facility. The security fencing is high-security. Surveillance system, barriers to vehicles, and security guards work in tandem to block entry by anyone who is not authorized.
But physical barriers on their own don't suffice. Modern facilities incorporate data Center Access Control Systems that control the entry of each gate as well as the checkpoint.
Biometric Identification Verification
Data Center Biometric Security has a significant role to prevent the possibility of unauthorized access. Techniques like fingerprint scanners and facial recognition as well as iris verification assure that only authentic individuals are allowed to enter restricted spaces.
Biometric Systems:
- Avoid sharing credential data
- Lower the threat of an insider
- Create detailed access logs
- Encourage the compliance of international standards
2. Secure internal Infrastructure
After entering the perimeter, further security features protect server rooms as well as network equipment. Multiple-factor authentication, smart card systems, and monitoring interconnection create layers of security within the internal perimeter.
Automated Security Monitoring
The latest Data Center Security Automation UAE Systems use algorithms driven by AI to analyse the activity of facilities. Automatic alerts identify suspicious movements and access requests that are unusual, and other operational anomalies.
Automated response reduces time to respond and provides 24/7 monitoring, without human errors. When working in highly populated digital environments, automation improves security as well as operational efficiencies.
3. Network as well as Cyber Defense Integration
Physical security should be aligned with sophisticated cyber-security strategies. Modern facilities have an extensive security of the network to protect data centres UAE to guard against data breaches, cyberattacks as well as malware intrusion.
These covers:
- Security systems and firewalls
- Segmented network architecture
- Assessments of vulnerability on a continuous basis
- Secure communication channels
Through the combination of physical barriers and cyber security, businesses can attain complete all-in-one security for their data centers UAE.
4. Data encryption and data protection
Although there is perimeter and network security in place, sensitive data should be secured when in transit or rest.
Data Center Encryption ensures that information in the database is not applicable without authorization. Security protocols for encryption protect sensitive information against internal misuse as well as external breach.
For UAE-based financial and government facilities, data encryption requirements are essential to ensure the compliance of regulators and to ensure trust.
5. Rapid Alerting and Responding to Threats
The traditional reactive security model is not sufficient anymore. Modern security systems rely on advanced data Center threat Detection methods that rely on the use of machine learning and behavioural analytics.
They are these systems:
- Recognize unusual activity patterns
- Flag unauthorized login attempts
- The ability to detect unusual network activity
- Generate real-time alerts
Proactive detection allows instant action, which reduces the time to repair and also preventing harm. If integrated in Data Center Security Automation UAE the threat detection can be a very powerful tool for predicting the future instead of merely a monitoring feature.
The most important components of a Multi-Layer Defence Strategy
In order to ensure the effectiveness of Security of the Data Center Perimeter Security, UAE organizations focus on balancing:
- Physical perimeter barriers
- Credential and biometric-based Data Center access Control
- Secure security of the network to protect data centers UAE
- Strong Data Center Encryption protocols
- Intelligent Data Center Threat Detection systems
The layered design minimizes the risk of weaknesses and improves the resilience to operational threats.
The UAE's Promise to Secure Digital Infrastructure
In the context of smart city initiatives, and the adoption of cloud services accelerates The UAE invests in the latest security systems. The regulations of the UAE government and standards for industry focus on proactive security and encourage facilities to implement Biometric security for Data Centers and automated technology.
Through a combination of physical, digital and automated defense, the United States makes sure that its infrastructure is safe from evolving threats to its global infrastructure.
Conclusion
In the age of digital change multi-layer perimeter security is crucial to safeguard the data centers in UAE. The combination of Data Center Perimeter Security with sophisticated Data Center Access Control and solid network security to protect the data center UAE provides a solid security foundation to protect against both cyber and physical threats. The integration with Data Center Security Automation UAE increases the monitoring accuracy as well as speed of response, and Data Center encryption ensures the security of sensitive data throughout the entire process. By proactively Data Center Threat Detection companies are able to anticipate and eliminate risks before they grow.
While the UAE remains a world leader in the field of digital technology by investing in comprehensive security of data centers UAE strategies will ensure the long-term stability, compliance and efficiency. Multi-layer protection is not merely an insurance policy, which is essential to maintain growth in the digital ecosystem.
FAQs
1.What is multi- layer perimeter security of data centres?
It's an effective security strategy that integrates biological, physical, network security and automation to ensure security at every level of the facility.
2. What is the reason Data Center Biometric Security important?
It ensures correct authentication of identity and blocks unauthorised access to or misuse of credential.
3. What is the best way to Data Center Security Automation UAE enhance security?
Automation allows immediate monitoring of security, speedier attack detection, and reduces errors made by humans.
4. What function does Data Center Encryption perform?
Encryption ensures that sensitive data is not accessed by an unauthorized individual whether in rest or transit.
5. How can network security for data centers UAE enhance physical security?
Safeguards IT infrastructures from cyber-attacks by providing protection throughout the entire process, in conjunction with physical security technology.
For more information contact us on:
Tektronix Technology Systems Dubai-Head Office
+971 50 814 4086
+971 55 232 2390
Office No.1E1 | Hamarain Center 132 Abu Baker Al Siddique Rd – Deira – Dubai P.O. Box 85955
Or click on the below link for more information:
https://tektronixllc.ae/data-center-perimeter-security-solutions/
