The Modern Guide to Data Center Security Across Oman and GCC
Our security system offers an entire security ecosystem, which integrates Data Center Access Control, Data Center Perimeter Security, Data Center Surveillance, Data Center Intrusion Detection, and Data Center Threat Detection into a single security system.
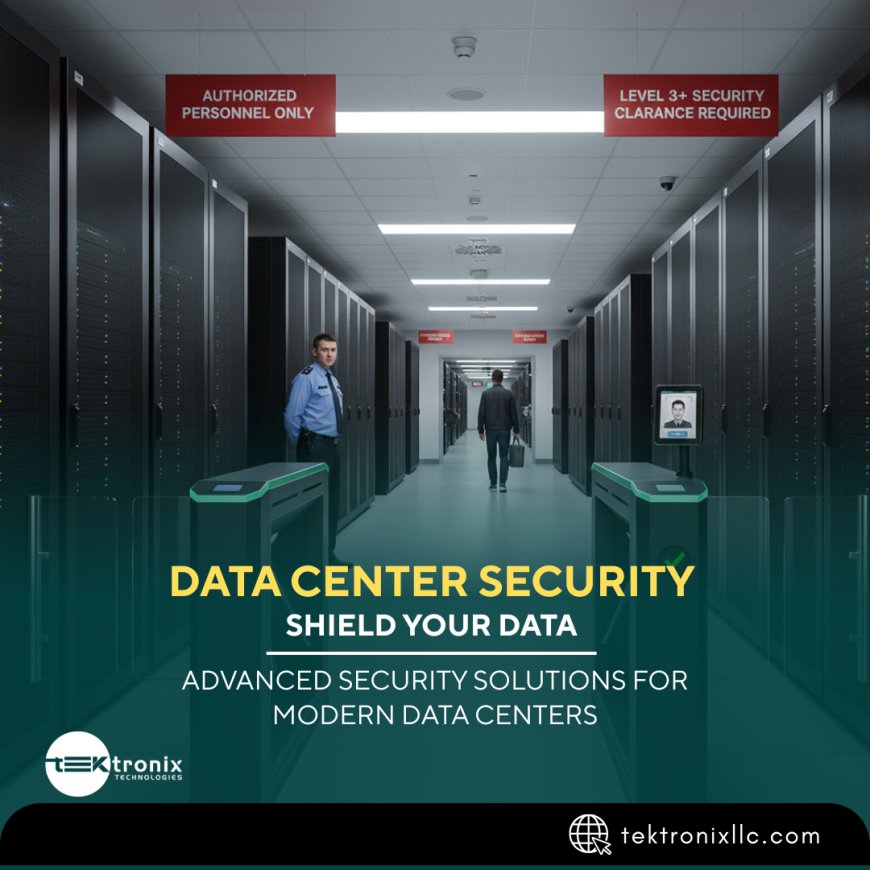
Due to the rapid increase in digital transformation in Oman and the GCC, data centers have become the foundation of government services, financial activities, cloud systems, and enterprise IT base. These are large-scale storage centers of sensitive data, and they need extensive security systems to avoid cases of unauthorized data access, cyber-attack, and disruption of operations.
We offer a multi-layered security solution based on the advanced Data Center Access Control, reinforced Data Center Perimeter Security, intelligent Data Center Surveillance, proactive Data Center Intrusion Detection, and real-time Data Center Threat Detection. This combined strategy makes the mission-critical infrastructure as secure as possible.
Strengthening Identity Verification with Data Center Access Control
The Data Center Access Control as the first level of protection to make sure only authorized personnel have access to sensitive locations like server rooms, network control centers, and equipment racks.
Key capabilities include:
- Biometric and card-based authentication
- Role-based access permissions
- Multi-factor authentication for critical zones
- Centralized access monitoring and logging
- Automated access alerts and reporting
Proper access control reduces the number of insider threats and secures the appearance of vital hardware infrastructure.
Defending Infrastructure with Data Center Perimeter Security
Strong Data Center Perimeter Security handles the external protection of the facility and prevents the entry of unauthorized access before the individual gets access to places of interest.
The perimeter protection measures involve:
- Secure fencing and controlled entry gates
- Vehicle access control systems
- Security checkpoints and guard monitoring
- Anti-tailgating entry systems
- Integrated alarm and monitoring solutions
There exist good perimeter controls because only the verified people and vehicles are allowed to come in the facility.
Continuous Monitoring with Data Center Surveillance
Advanced Data Center Surveillance also offers 24/7 surveillance around the facility by use of intelligent video systems.
Capabilities in surveillance comprise:
- High-definition CCTV cameras
- AI-powered video analytics
- 24/7 monitoring and recording
- Real-time alerts for suspicious activities
- Secure video storage and retrieval
The surveillance systems will allow complete visibility and increase situational awareness in the data centers.
Proactive Protection with Data Center Intrusion Detection
To prevent the illegal access, we implement advanced Data Center Intrusion Detection systems that help to identify the intrusion attempts or abnormal behaviour in real-time.
The intrusion detection features are:
- Motion sensors and vibration detectors
- Rack-level intrusion monitoring
- Door and cabinet tamper alerts
- Integrated alarm systems
- Automated incident notifications
Advance intrusion detection prevents breach of security even before it gets serious.
Intelligent Monitoring with Data Center Threat Detection
Security threats may arise physically and digitally. Data Center Threat Detection systems continuously analyze system activities and environmental conditions in order to be able to detect any potential risks.
Threat detection capabilities consist of:
- Real-time anomaly detection
- Behavioural analytics
- Environmental monitoring (temperature, humidity)
- Centralized security dashboards
- Automated escalation protocols
Threat detection in real-time increases operational resilience and eliminates downtime.
Integrated Multi-Layer Data Center Security Architecture
Our security system offers an entire security ecosystem, which integrates Data Center Access Control, Data Center Perimeter Security, Data Center Surveillance, Data Center Intrusion Detection, and Data Center Threat Detection into a single security system.
This combined strategy makes it possible to:
- Centralized monitoring and control
- Real-time incident response
- Enhanced compliance and audit readiness
- Reduced security vulnerabilities
- Scalable deployment across multiple data centers
Layered security is applied in a manner that ensures that a single vulnerability does not affect the whole facility.
Enhancing Operational Efficiency Through Automation
The operations of modern data centers cannot be performed without automation. Our smart security systems assist organizations to:
- Reduce manual monitoring requirements
- Improve incident response time
- Automate reporting and compliance tracking
- Maintain accurate access and activity logs
- Increase operational efficiency
Automation provides stability in the security performance and better management.
Future-Ready Data Center Security Innovation
The information security in data centers has to evolve with the advanced technologies as the digital infrastructure continues to spread-out all-over Oman and the GCC.
The emerging innovations are:
- AI-powered threat detection
- Cloud-integrated security platforms
- Predictive analytics for risk prevention
- Smart sensor-based monitoring
- Scalable modular security architecture
Future ready security solutions guarantee flexibility and future security.
Conclusion
The multi-layered security plan is necessary to obtain modern data centers in Oman and the GCC. To ensure the safety of key infrastructure elements, business continuity, and the security of critical data centers, organizations may apply high-quality Data Center Access Control, powerful Data Center Perimeter Security, smart Data Center Surveillance, active Data Center Intrusion Detection, and active Data Center Threat Detection. These colliding solutions generate resilience of the security, operational performance, and offer security to the digital backbone of the modern businesses.
FAQs
1. What is the importance of Data Center Access Control?
Data Center Access Control allows access into sensitive areas by authorized individuals ensuring the protection of servers and IT infrastructure.
2. What does Data center perimeter Security entail?
The Data Center Perimeter Security encompasses fencing, controlled access gates and surveillance systems to keep boundaries of the facilities secure.
3. What is the purpose of Data Center Surveillance?
Data Center Surveillance involves camera and monitoring to trace the activities and unhealthy behaviours.
4. What does Data Center Intrusion Detection mean?
Data Center Intrusion Detection is a tool that identifies unauthorized access attempts by detecting sensors and alarms.
5. What is the purpose of Data Center Threat Detection?
Data Center Threat Detection is used to examine the system activity and environmental data in order to determine the possible risk and security threats.
For more information contact us on:
Tektronix Technology Systems Dubai-Head Office
+971 55 232 2390

 afroztek
afroztek